For a business leader like yourself, safeguarding your organization’s data is a top priority. Data breaches can erode customer trust, damage your reputation, and ultimately affect your bottom line. Taking a proactive approach to data security demonstrates your commitment to protecting valuable information and fostering a culture of security awareness within your organization. This blog […]
Steps you can take to elevate your cybersecurity posture

Safeguarding your organization’s data and infrastructure is crucial. With cyberthreats becoming increasingly complex, a proactive cybersecurity strategy is no longer optional. Learn proactive measures that can help mitigate risk, ensure business continuity, and empower you to make informed decisions for your organization’s future in this blog. Benefits of proactive cybersecurity Proactive cybersecurity is a strategic […]
Empower your team with these essential email security tips

Many cyberattacks use email to gain access to systems, which underscores the critical need for businesses to prioritize email security. Here are some practical tips you can employ to protect your organization from evolving threats and ensure the confidentiality of your sensitive information. Use strong passwords Many email users fail to realize how important it […]
A proactive approach to cybersecurity in the Gen Z workplace

The influx of Gen Z talent into the workforce brings a wealth of digital expertise. However, their digital experience may include areas requiring additional security awareness. This blog will explore practical solutions to ensure smooth employee integration while maintaining a robust cybersecurity framework. With 2024 rolling on, the Gen Z workforce is poised to join […]
A guide on the 3 types of hackers and how they operate

The term “hacker” often conjures up images of criminals in hunched over computers in a dark room, but in the 1950s, hackers were simply computer enthusiasts who enjoyed pushing boundaries. However, the rise of personal computers in the 1980s led to a shift. Hackers in the ’80s, often teenagers, exploited vulnerabilities in systems, sometimes targeting […]
Online security essentials: Protecting your digital footprint

The internet has become an essential tool for businesses of all sizes. It allows them to connect with customers, manage operations, and access valuable information. However, this digital dependency comes with a rising threat: cyberattacks. Malicious actors are constantly coming up with new ways to steal data, infect devices, and disrupt operations. Fortunately, by implementing […]
Prevent cyberattacks from inflicting financial losses with cyber insurance

Small businesses face a growing challenge in securing their data and operations in today’s digital age. The prevalence of cyberattacks highlights the importance of an effective cybersecurity strategy. Essential elements include firewalls, data backups, and regular cybersecurity awareness training for employees. However, a holistic approach should also consider cyber insurance. This financial instrument provides an […]
Strengthen your passwords with NIST guidelines
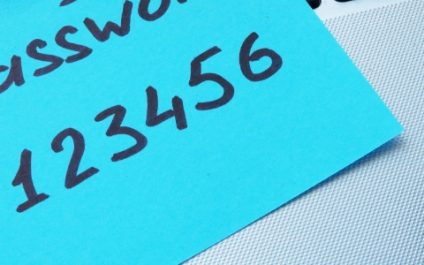
Many users unknowingly create weak passwords or mishandle them through common habits, leaving their data and accounts vulnerable to breaches. To combat this vulnerability, the National Institute of Standards and Technology (NIST) offers clear guidelines for crafting strong passwords and good practices to ensure password integrity. What is NIST? NIST is a US government agency […]
Top 5 gateways and vulnerabilities that lead to security breaches

IT-forward businesses operate more efficiently and precisely than ever before, but if they’re not taking the necessary precautions, they can also be vulnerable to more cyberattacks. With more devices connected to the internet today, it’s essential to be aware of the most common weak points that hackers use to breach your systems. Social engineering Social […]
Is it worth monitoring employees online?

The digitization of the workplace has opened up new frontiers for employer oversight. With workers more connected than ever through computers and internet-based tools, companies are exploring the advantages of monitoring for optimizing workflow and enhancing productivity. Yet, this digital vigilance prompts a crucial discussion about where to draw the line between legitimate business interests […]



